casey was able to narrow the bug down to one area of code, and even provided some test cases for you to work with to get started. the two accounts in testsomeusersthatwork are working as expected and saving successfully. the three accounts in testsomeusersthatfail should be saving, but they are not, which is why they incorrectly return false right now. javascript
Answers
Casey was able to narrow the bug down to one area of code, and even provided some test cases for you to work with to get started. The two accounts in `testSomeUsersThatWork()` are working as expected and saving successfully. The three accounts in `testSomeUsersThatFail()` should be saving, but they are not, which is why they incorrectly return false right now. This is a problem with the code that handles saving the accounts in the database.
To fix it, you should look at the code in the `save()` function, which is called by both `testSomeUsersThatWork()` and `testSomeUsersThatFail()`. Specifically, you should look at how the accounts are being saved in the database and try to identify the problem with the code. Once you have identified the problem, you can then modify the code to fix it and verify that both `testSomeUsersThatWork()` and `testSomeUsersThatFail()` are now working correctly.
Know more about database here:
https://brainly.com/question/30634903
#SPJ11
Related Questions
_____ is the feature that allows you to quickly advance cell data while filling a range of cells.
A. Auto Fill
B. AutoCopy
C. FillAuto
D. CopyAuto
Please no files just type the answer, thanks!
Answers
Answer:
A. Auto Fill
Explanation:
Auto Fill is the feature that allows you to quickly advance cell data while filling a range of cells.
you have a system that will not boot. what would be the first step in trying to resolve the issue?
Answers
The first step in trying to resolve a system that will not boot would be to troubleshoot the issue.
The first step would be to identify the symptoms of the issue. This could include the computer not turning on, the screen remaining blank, or an error message appearing. Once the symptoms have been identified, the next step would be to isolate the cause of the issue. This could be done by checking the power supply, ensuring that all cables and connections are secure, and running a diagnostic test on the hard drive.
If these steps do not resolve the issue, the next step would be to check the system BIOS settings. The BIOS is responsible for controlling the boot process, so any changes to these settings could cause the system to fail to boot. Checking the BIOS settings could involve resetting the BIOS to its default settings, updating the BIOS firmware, or adjusting the boot order.
If none of these steps resolve the issue, the next step would be to try and boot the system in Safe Mode. Safe Mode is a diagnostic mode that starts the computer with a minimal set of drivers and services. This can help to isolate the cause of the issue and allow for further troubleshooting. In summary, the first step in trying to resolve a system that will not boot would be to troubleshoot the issue by identifying the symptoms, isolating the cause of the issue, checking the BIOS settings, and trying to boot in Safe Mode.
Know more about troubleshoot here:
https://brainly.com/question/30033227
#SPJ11
write a program to enter base and height of a triangle and print area of rectangle using Q Basic. (class8)
Answers
Answer:................................
Cls
Input " enter the base";b
Input" enter the height ";h
A = b*h
Print" the area of triangle=" ;a
End
Which of the following is a primary drawback to the "do anything anywhere" computing environment?
It makes work environment less pleasant.
It creates a digital divide.
It centralizes power at corporate headquaters.
It blurs the traditional boundaries between work and family time.
Answers
The primary drawback to the "do anything anywhere" computing environment is that it blurs the traditional boundaries between work and family time.
With the ability to work remotely from anywhere and at any time, it can be difficult for individuals to separate their work and personal life. This can lead to burnout, increased stress, and an unhealthy work-life balance.
While there are many benefits to the "do anything anywhere" computing environment, such as increased flexibility and productivity, there are also several drawbacks. One of the primary drawbacks is that it blurs the traditional boundaries between work and family time. In the past, individuals would typically go to work during designated hours and then come home to their families. However, with the ability to work remotely, it can be difficult to separate work from personal life. This can lead to individuals feeling like they are always "on the clock" and struggling to find a balance between their work and personal responsibilities.
To know more about do anything anywhere visit :-
https://brainly.com/question/14704528
#SPJ11
if the wide area network (wan) is supporting converged applications like voice over internet protocol (voip), which of the following becomes even more essential to the assurance of the network? a. boundary routing b. classless inter-domain routing (cidr) c. internet protocol (ip) routing lookups d. deterministic routing
Answers
if the wide area network (wan) is supporting converged applications like voice over internet protocol (voip) internet protocol (ip) routing lookups will be even more essential to the assurance of the network.
Understanding WAN
WAN stands for Wide Area Network is a network that is used as a network that connects between local networks. Local computer networks are not only physically adjacent to each other, but share the same group of IP addresses.
The local network can be one room, one office or even one city. While the WAN itself is a network that connects these local networks within a city, province or even between countries. The difference between WAN and LAN networks is in the type of media used. Generally local networks or LANs use similar network media.
While the WAN is connected to devices with different transmission media and protocols. The WAN coverage area is also very wide, but unites the network as if it were in one room. WAN networks have lower data transfer rates than local networks or LANs. WAN network technology relies on companies providing long-distance telecommunications services. WAN networks use many kinds of network technologies with a mix of analog and digital signals for data transmission. Of course this is different from a local network or LAN which uses a connection between computers that are physically connected to each other with the same protocol and transmission media. The components in the WAN and their functions will be discussed later.
Learn more about WAN at https://brainly.com/question/14793460.
#SPJ4.
A location that has all the equipment installed but does not have active Internet or telecommunications facilities, and does not have current backups of data, is an example of a:
Answers
A location that has all the equipment installed but does not have active Internet or telecommunications facilities, and does not have current backups of data is an example of an offline location or an isolated site.
It is typically set up as a backup or a disaster recovery site to be used in case the primary site becomes unavailable due to a natural disaster, power outage, or other unforeseen circumstances.
Offline locations are designed to replicate the capabilities of the primary site as closely as possible, including the hardware, software, and data. This allows for a seamless transition of operations to the backup site when necessary. However, because the site is not connected to the internet or telecommunications facilities, data cannot be backed up to remote locations, and access to data and applications is limited to local users.
To ensure that an offline location is effective in the event of a disaster, it is important to regularly test the site and its capabilities, including backup and recovery procedures, network connectivity, and user access.
Learn more about equipment here:
https://brainly.com/question/30453915
#SPJ11
A bakery has hired you to create a logo. They are looking for a logo that they can layer over images without covering anything in the background. Which file format should the photographer choose to deliver the photo? Explain why.
Answers
A bakery has hired a professional to create a logo. They are looking for a logo that they can layer over images without covering anything in the background. The file format that the photographer should choose to deliver the photo is Portable Network Graphic (PNG) format.
What are the advantages of the PNG format?The fundamental benefit of PNG over JPEG is that the compression is lossless, which means that there is no loss in quality when a file is opened and saved several times. PNG is also suitable for pictures with great contrast and detail.
Millions of color combinations are possible with 24-bit color (true color). The alpha channel in the 32-bit RGBA enables for extra color gradients and transparencies with vast color possibilities. PNG pictures are smaller and load faster than GIF or RGB TIFF images.
Learn more about PNG:
https://brainly.com/question/20293277
#SPJ1
why do most operating systems let users make changes
Answers
By these changes you most likely are thinking of the term 'Over Clocking'
Over Clocking is used on most Operating Systems to bring the item your over clocking to the max.
Over Clocking; is mostly used for Crypto mining and gaming.
Ummmm pls helppp
Which are the features of conditional formatting?
Conditional formatting enables you to_______
and_______
Answers
Answer:
A conditional format changes the appearance of cells on the basis of conditions that you specify.
Explanation:
If the conditions are true, the cell range is formatted; if the conditions are false, the cell range is not formatted. There are many built-in conditions, and you can also create your own (including by using a formula that evaluates to True or False).
What is the sticker price for a vehicle with these features and costs: suggested retail price of $15,150, destination charge of $359, equipped with air conditioning, tinted window, and a custom sound system for $800, $210, and $490, respectively?
Answers
The sticker price of a vehicle is an important factor to consider when purchasing a car. It is the total cost that includes the suggested retail price and additional charges for any features or options. The sticker price for the vehicle with all the given features and costs is $17,009.
To determine the sticker price for a vehicle with the given features and costs, we need to add the suggested retail price of $15,150, the destination charge of $359, and the costs of the added features - air conditioning for $800, tinted window for $210, and a custom sound system for $490.
So, the total cost would be:
$15,150 (suggested retail price)
+ $359 (destination charge)
+ $800 (air conditioning)
+ $210 (tinted window)
+ $490 (custom sound system)
= $17,009
Therefore, the sticker price for a vehicle with these features and costs would be $17,009.
In conclusion, it is important to consider the sticker price when purchasing a vehicle. By adding the suggested retail price, destination charge, and any additional costs for features, we can determine the total cost and sticker price for a vehicle.
To learn more about sticker price, visit:
https://brainly.com/question/21281556
#SPJ11
who created apple and in what year was it created
Answers
Answer:
Steve Jobs founded Apple and it was founded on April 1, 1976
Explanation:
I think you mean the Apple Store but uh-
Answer: Apple was created by Steve jobs, Steve wozniak,Ronald wayne. It was created in april 1,1976.
Explanation:
Pleaseee need help ASAP!!
Will mark BRAINLIEST!! :)

Answers
Answer:
The correct option is Option B
Explanation:
We need to find examples of client-side code.
Client Side code: The part of code, that doesn't require server for performing specific task
SO, The correct option is Option B
Prompt for special characters in user name
Reason: We can use alert to generate prompt using JavaScript or through validation and it can be done on client side.
All other options, we need to hit the server to perform the task, So they are not client-side code.
Describe the four techniques mentioned in the article that help you, the speaker, keep your audience engaged
Answers
Answer:
This is what the online content site says:
Explanation:
Analyze and Adapt to Your Audience
The key focus of speech development is to always consider your audience. The audience is the reason for the speech; so much of the preparation requires analyzing the audience. However, preparing for your audience isn’t simply learning about your audience. It is figuring ways to adapt to your audience to ensure that they remain engaged throughout your speech. After all, there is nothing worse then losing your audience halfway through the speech.
What is the best way to maintain audience engagement? By incorporating these techniques into your speech.
Begin with a Question
One way to hook your audience at the beginning of the speech is to start with a question. This helps get the audience thinking immediately, and also shows that you are there to interact with the audience.
Often, the type of question you want to ask is one that audience members can quickly answer. For example, you might ask, “If you had to make a choice, which would you prefer to do—exercise 20 every day or sit with a good book every day? How many of you would choose to exercise? How many of you would prefer to read?” Not only does it cause the audience to become part of the speech, people in the audience start building connections. They see people who are similar to them. This also helps you build an understanding of the audience. You can actually learn about your audience by sitting back and seeing how people respond to your question.
One way to get an audience engaged is to ask a question and seek a response.
Break the Ice
If you want to get you audience energized and have them participate in your speech, one thing you can do is use an icebreaker. An icebreaker is any activity you incorporate that gets your audience moving around or interacting with their neighbors. The activity should involve movement, interaction, or both. It could be a quick survey, such as, “If your favorite season is summer, head to the back of the room and share one reason why with a neighbor. If you favorite season is winter, head to the front of the room and share one reason why with a neighbor.” Or, it could simply be a turn and talk to you neighbor about a topic related to the speech. Engaging the audience is one way to get them interested.
Icebreakers can also be used for a long speech. Because most listeners’ attention spans will drift after about 10 minutes, adding one of these to a speech can keep the momentum going. Another thing to know about icebreakers is that they work well after a break, such as a snack or lunch break. Keep in mind that not everyone enjoys icebreakers and that they can make some people uncomfortable. So, it is best to avoid them at the beginning of a speech if possible, unless, of course, people need to get to know each other as part of your speech.
Text icebreakers are one way to engage the audience.
Seek the Wisdom of the Audience
Another valuable way to include the audience and keep them engaged is to ask for audience input. By doing this, audiences actually contribute to the presentation. The easiest way to do this is to use some type of media displayed in the room, such as a transparency displayed on an overhead projector or a LCD-projector showing a document. Then, have audience members share ideas that you can type or write and display for all to see. For example, suppose your speech was about the history of the Summer Olympic Games. You might ask audience members to share their answers to the following question “What sports appear in the modern Summer Olympic Games?”
To maintain engagement, have audience members share their ideas or knowledge.
Keep the Audience Focused
One final way to keep the audience focused is to make frequent eye contact with many different members. This makes the message more personal and helps audience members feel you are talking directly to them. Making eye contact can be difficult, but one trick expert speakers use is to look slightly above the actual audience members’ heads. This way, it looks like to you are making eye contact without being awkward.
Humor can also be helpful to engaging the audience. Laughter puts people at ease and keeps the speech light. Always make sure that the humor is appropriate, respectful, and something the audience will understand.
Presenting speeches is hard work, and it can be a challenge to keep your audience thoughtfully engaged. By using these suggestions, you will be able to maximize your audience’s attention while minimizing their distractibility.
The four techniques are:
Describe a scenario or a character.Do Tell a story.Do Share your own personal experience.Link the topic to a a recent event.Why is audience engagement?The act of good engaging of an audience is one that boost participation, and also boost learning and increase satisfaction.
Therefore, The four techniques are:
Describe a scenario or a character.Do Tell a story.Do Share your own personal experience.Link the topic to a a recent event.Learn more about techniques from
https://brainly.com/question/2183813
#SPJ1
Given the doubt and uncertainty of a relational exchange, what is necessary to ensure the customer's ongoing commitment to the Spero brand?
Answers
The factor that is necessary to ensure the customer's ongoing commitment to the Spero brand is that:
Know your Customer Expectations.Study your Customer types and Journeys.Examine How Brand Perception Has been altered Over Time, etc.How do one show commitment to customers?This can be done by:
Giving your customer relevant and valuable content/brand.Form a customer community.Share success stories linked to the brand.Therefore, The factor that is necessary to ensure the customer's ongoing commitment to the Spero brand is that:
Know your Customer Expectations.Study your Customer types and Journeys.Examine How Brand Perception Has been altered Over Time, etc.Learn more about brand from
https://brainly.com/question/25689052
#SPJ1
The average lease payment for a new vehicle is just over $450 per month for a three-year...
Answers
Answer:
it depends on your insurance company
Explanation:
Artificial intelligence (ai) in perspective is a complex and interdisciplinary field that involves several specialties, including:
Answers
Artificial intelligence (ai) in perspective is a complex and interdisciplinary field that involves several specialties, including Interdisciplinary research diploma applications integrate or greater conventional educational guides of have a look at right into a greater personalized major.
What is Interactions among AI Artificial intelligence?Interactions among AI Artificial intelligence and schooling is but some other instance of interdisciplinarity in AI (Oudeyer et al., 2016), that may immediately gain now no longer best the 2 fields, schooling and AI, however society and productiveness as a whole.
Interdisciplinary research diploma applications integrate or greater conventional educational guides of having a look at right into a greater personalized major. Unlike a liberal arts diploma wherein you'll have a look at an extensive type of subjects, an interdisciplinary diploma lets in college students to discover a greater centered subject matter that crosses into more than one field.Read more about the interdisciplinary :
https://brainly.com/question/25955559\
#SPJ1
96) One of the capabilities of Internet communication is the ability of the individual to appear essentially anonymous by using made-up user names. Is anonymity the same thing as privacy, and should it be a right? What ethical issues are raised by increased anonymity?
Short Answer:
Answers
Anonymity and privacy are related but distinct concepts. The right to anonymity and privacy raises ethical issues, particularly in the context of the Internet. Anonymity allows individuals to express their opinions without fear of retribution, promoting freedom of speech and fostering open discourse.
Anonymity refers to the ability to conceal one's identity, while privacy entails control over one's personal information and how it is shared. Both are considered essential aspects of personal freedom, but they differ in scope and focus. However, Anonymity also enables harmful behaviors, such as cyberbullying, trolling, and criminal activities, as perpetrators can hide behind a veil of anonymity.
Balancing the rights to anonymity and privacy with the need for security and accountability is a complex ethical challenge. Protecting individual freedoms while maintaining the safety and integrity of online communities requires careful consideration of the trade-offs between these values. Developing policies and technologies that balance these interests is crucial for promoting a responsible and ethical internet experience.
You can learn more about Anonymity at: brainly.com/question/21832686
#SPJ11
Please helpp!! I need it quickly!

Answers
Answer:
a
Explanation:
what is coding? Explain
Answers
Answer:
coding is the process of transforming ideas, solutions, and instructions into the language that the computer can understand
Explanation:
Answer:
Coding is learning and using computer’s language for your favor, when you code, you make the computer/device under your control.You are presenting your ideas to the computer using it’s language, just like talking to a friend that doesn’t understand your language, and u learn his. Coding can help make games and websites, by using the computer’s language to manually make the page. Coding can also enable someone to know information he isn’t supposed to be informed by, like someone’s location or bank account. Coding can help create sites that not everyone is able of doing, because it is the hard way to make a site 100% the way you want it to be.
ur wlcm :)
brainliest?
A nested "if" statement only executes if the "if" statement in which it is nested evaluates to True. True False
Answers
The given statement "a nested "if" statement only has an impact if the "if" statement it is contained within evaluates to True" is TRUE.
What is a nested "if" statement?The use of nested IF functions, or one IF function inside another, increases the number of outcomes that may be tested and allows for the testing of numerous criteria.
Based on their performance, we wish to assign each student a grade.
Return an A if Bob's score in B2 is greater than or equal to 90.
Only if the "if" statement in which it is nested evaluates to True does a nested "if" statement take effect.
The OR function allows you to test many conditions in each IF function's logical test and returns TRUE if any (at least one) of the OR arguments evaluates to TRUE.
Therefore, the given statement "a nested "if" statement only has an impact if the "if" statement it is contained within evaluates to True" is TRUE.
Know more about the nested "if" statement here:
https://brainly.com/question/14915121
#SPJ4
calculate the summary statistics for each of the two simulations (for example, by adding two more columns to the tab titled "summary of findings")
Answers
In order to calculate the summary statistics for each of the two simulations, we can add two more columns to the tab titled "Summary of Findings".
Summary statistics is the method of analyzing and summarizing data. In statistical analyses, it plays an essential role. It provides a brief overview of the data that has been collected.The summary statistics are listed below. Since we don't have the exact data, let's pretend that there are two sets of data available; let's call them Set A and Set B. We need to determine the mean, median, mode, range, standard deviation, and variance for each set. Here are the summary statistics for Set A and Set B: Set A Mean: To find the mean, add up all of the numbers in the set and divide by the total number of items. Median: The median is the middle number in the set. Mode: The mode is the number that appears the most often in the set. Range: The range is the difference between the largest and smallest numbers in the set. Standard deviation: Standard deviation is a measure of how spread out the numbers in the set are. Variance: Variance is a measure of how much the data deviates from the mean. Set B Mean: To find the mean, add up all of the numbers in the set and divide by the total number of items. Median: The median is the middle number in the set. Mode: The mode is the number that appears the most often in the set. Range: The range is the difference between the largest and smallest numbers in the set. Standard deviation: Standard deviation is a measure of how spread out the numbers in the set are. Variance: Variance is a measure of how much the data deviates from the mean. This will give us a good understanding of the data we're dealing with and assist us in making more informed choices when interpreting results or drawing conclusions.
To know more about statistics visit:
https://brainly.com/question/32201536
#SPJ11
What behavior do elements in a stack follow?
Answers
Answer:
last in, first out, or LIFO behavior
Explanation:
B
which meaning does the abbreviation c/c represent?
Answers
The phrase "carbon copy" alludes to the message's recipient whose location appears after Cc: header.
What does CC stand for?Carbon copies: To let the recipients of a business letter know who else received it, a cc designation would be placed at the bottom of the letter, followed by the names of those who received carbon copies of the original. The term "cc" in emails refers to the additional recipients who received the message.
A typical email will have a "To" box, a "CC" field, and only a "BCC" section that allows you to enter email addresses. The abbreviation for carbon copy is CC. "Blind carbon copy" is what BCC stands for. The abbreviation BCC stands in blind carbon copy, while Cc stands for carbon copy. When copying someone's email, use Cc for copy them openly or Bcc to copy them secretly.
To learn more about carbon copy refer to :
brainly.com/question/11513369
#SPJ4
What is a Binary Operator?
Answers
A binary operator is a mathematical or logical operator that operates on two operands or values to produce a result. In other words, it's an operator that operates on two values to generate a new value.
Explanation:
What is an operator?
An operator is a symbol or a sign that represents a certain type of mathematical or logical operation to be performed on one or more operands, resulting in a final value.
A binary operator, on the other hand, works with two operands to produce a final value or result. For example, in the expression “4 + 5,” the addition operator (“+”) is a binary operator since it works on two values or operands (4 and 5) to produce the final value of 9.
Here are some examples of binary operators:
Multiplication (*): It is used to multiply two values. Subtraction (-): It is used to subtract one value from another.Division (/): It is used to divide one value by another. Addition (+): It is used to add two values.Learn more about operators here:
https://brainly.com/question/29949119
#SPJ11
Why are digital computers more popular these days?
Answers
Answer:
The small size of the transistor, its greater reliability, and its relatively low power consumption made it vastly superior to the tube.
what is not one of the advantages that can be provided when implementing the server-based network model?
Answers
The advantages that can be provided when implementing the server-based network model are Increased security of data stored on the server.
What is server?A server is a computer system that provides services to other computer systems or users in a network. It is a physical or virtual machine with an operating system, which is responsible for managing all the resources and services in the network. The server can provide services such as web hosting, file sharing, printing, email, application hosting, database hosting, and much more. The server is a powerful computer that is able to process large amounts of data and respond quickly to requests from the network. By using a server, organizations can easily store and manage large amounts of data, and make it available to their users. Servers are also used for hosting websites, allowing users to access the website from any device and location.
To learn more about server
https://brainly.com/question/27960093
#SPJ4
What is the default extension of Q Basic program file?
Answers
Answer:
Bas
Files written with QBASIC must be run using the program and have the "bas" file extension.
Hope this helps
#Carryonlearning
Complete the following sentences by choosing the best answer from the drop-down menus. A/an _______ is a device used to protect computer against surges and spikes in power. Sleep and Hibernate are examples of _______. Regular maintenance on a computer is good for _______. Bad sectors are sections of the _______ that are physically damaged. To protect some devices such as flash drives and external hard drives from corruption, it’s best to _______ the devices.
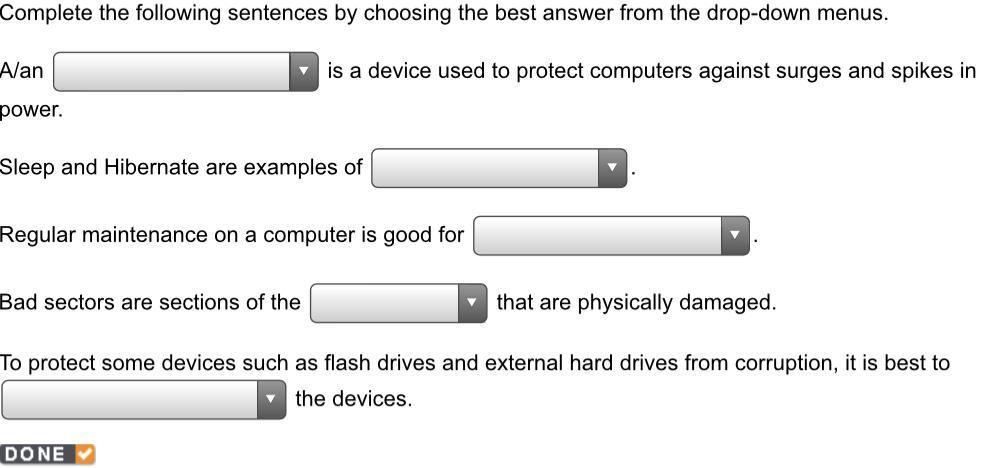
Answers
Answer:
1. Surge protector
2. Power-saving mode
3. Hardware and software
4. Hard disk
5. Eject
Explanation:
sadly my answer has deleted here so i have to start all over again
Which of the following is the only way to know exactly what your website will look like and whether it will work when published? Choose the answer.
A. Vewing it in Dual view
B. Viewing it in Wysiwyg view
C. Viewing it in Source view
D. Publishing it
Answers
D: "Publishing it" is the only way to know exactly what your website will look like and whether it will work when published.
Publishing the website is the only way to see exactly what it will look like and how it will function when it is live. Dual view, Wysiwyg view, and Source view are all ways to preview and edit a website before publishing, but they do not provide an exact representation of the final product.
Publishing the website allows you to see how all the different elements of the website work together, including links, images, and interactive features. This is especially important for testing the website's functionality and ensuring that it is user-friendly and easy to navigate.
The correct answer is D. Publishing it.
You can learn more about website at
https://brainly.com/question/25817628
#SPJ11
which term refers to an authentication and integrity protocol designed to prevent bad guys from impersonating legitimate dns servers?
Answers
The term refers to an authentication and integrity protocol designed to prevent bad guys from impersonating legitimate dns servers is DNS Security Extensions.
What is DNS Security Extensions?
DNSSEC uses digital signatures based on public key cryptography to strengthen authentication in DNS. With DNSSEC, the DNS data itself is signed by the data owner, rather than the DNS queries and responses themselves being cryptographically signed. Save the log. DNSSEC is a protocol that includes authentication of DNS responses. An attacker cannot use DNS to send a user to a malicious website, as authenticated responses cannot be forged or altered.
Learn more about DNS security: https://brainly.com/question/28414678
#SPJ4